The Un-Lovable Security Crisis

Is Your Business Infrastructure Built on a House of Cards? Every business owner today wants to move fast. New “vibe-coding” platforms promise to turn a simple idea into a functional app in minutes. While this speed feels like a competitive advantage, it often masks a terrifying reality: these apps frequently lack foundational security. If you […]
Microsoft Defender and SharePoint Vulnerabilities
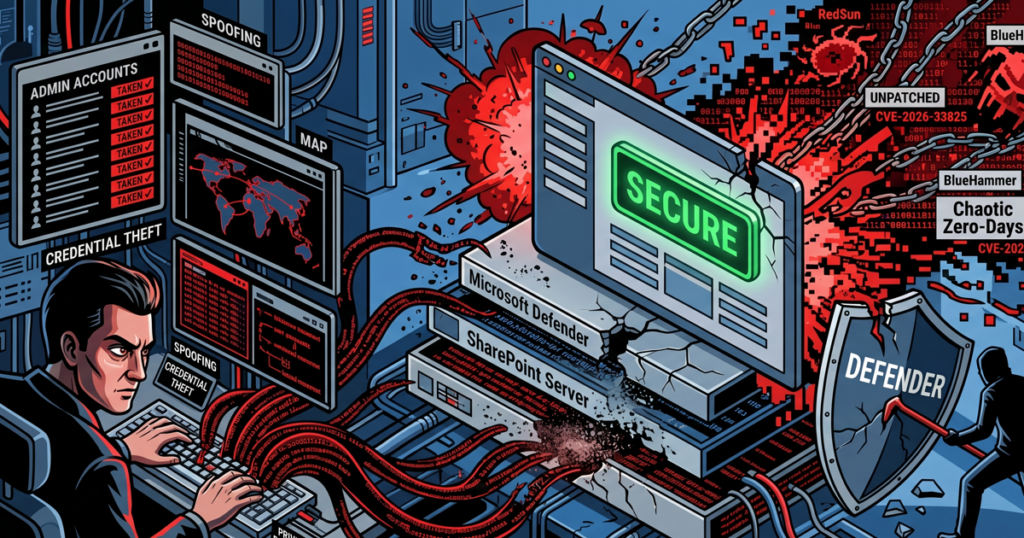
Weaponized Security Tools and the Illusion of a “Green” Dashboard Your security software now acts as a potential entry point for attackers. We face a new reality where standard tools like Microsoft Defender and SharePoint, designed to protect your network, now harbor “Chaotic” zero-day vulnerabilities. Attackers actively weaponize these flaws to steal credentials and seize […]
