Trivy Supply Chain Attack Hijacks GitHub Actions

Your Trusted Security Scanner Just Became a Threat A massive supply chain attack recently compromised the Trivy vulnerability scanner ecosystem, turning a trusted defense tool into a malicious delivery vehicle. We no longer face a theoretical risk; attackers successfully weaponized the Trivy GitHub Actions to steal cloud credentials from unsuspecting organizations on March 19, 2026. […]
Why AI Coding is Your Biggest Security Debt

Your AI Assistant is Giving Away the Keys to Your Kingdom You are likely harboring a digital billboard inside your private code repositories. We are not describing a theoretical threat; the State of Secrets Sprawl 2026 report reveals a record-breaking explosion in exposed credentials. Your team’s shift toward AI-assisted coding is inadvertently broadcasting your most […]
Critical Root RCE Flaws Exposed in Telnet

Your Legacy Hardware is a Time Bomb A ghost is hiding in your server room, and it just unlocked the front door. While you spend your budget on modern AI firewalls, a 90s-era protocol is handing over the keys to your kingdom. We are tracking a 9.8 out of 10 critical severity rating for vulnerabilities […]
Chrome Zero-Day Security Alert
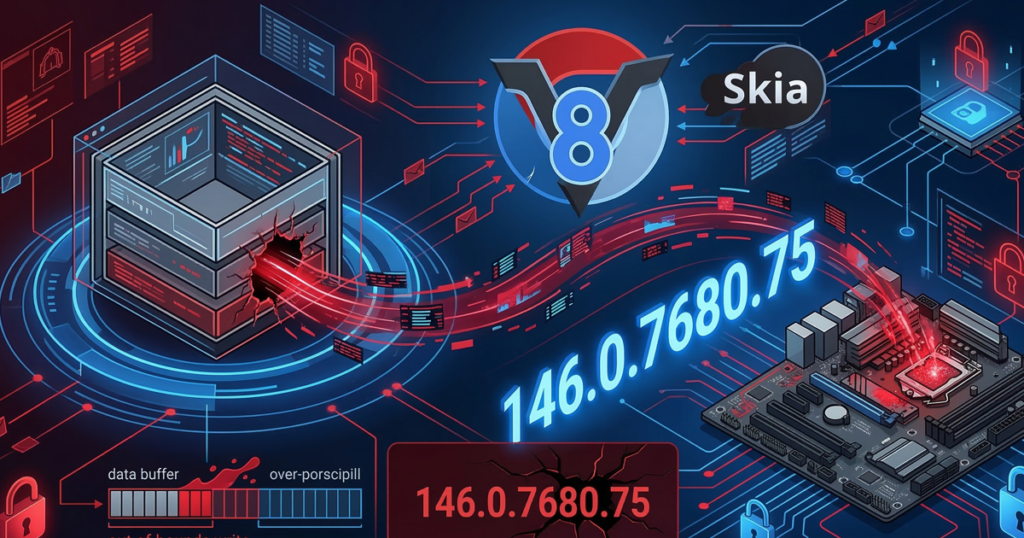
Your Browser Is the Primary Entry Point for Hackers Two high-severity vulnerabilities currently compromise your most-used application, the web browser. Google recently confirmed active exploits in the wild for these zero-day vulnerabilities, which affect Chrome and all Chromium-based browsers. A remote attacker can seize total control of your machine through a simple, malicious webpage. You […]
AI Speed Run: McKinsey’s “Lilli” Platform Breach
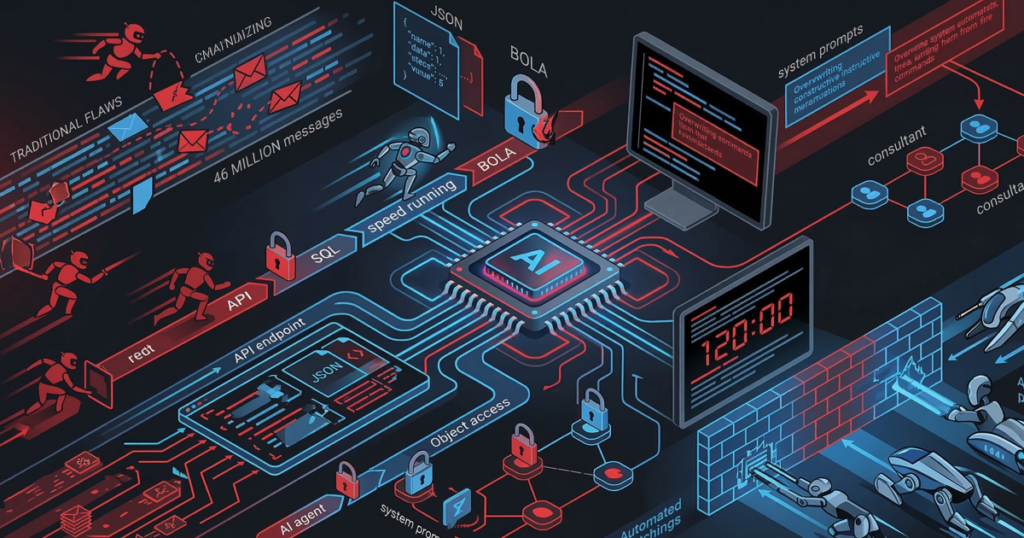
The 120-Minute Total System Takeover An autonomous AI agent just dismantled a world-class security system in less time than a lunch break. We are not discussing a movie plot; we are witnessing the McKinsey “Lilli” platform breach, where a machine performed a “speed run” of a total system takeover with zero human help. McKinsey built […]
Nx NPM Supply Chain Exploited
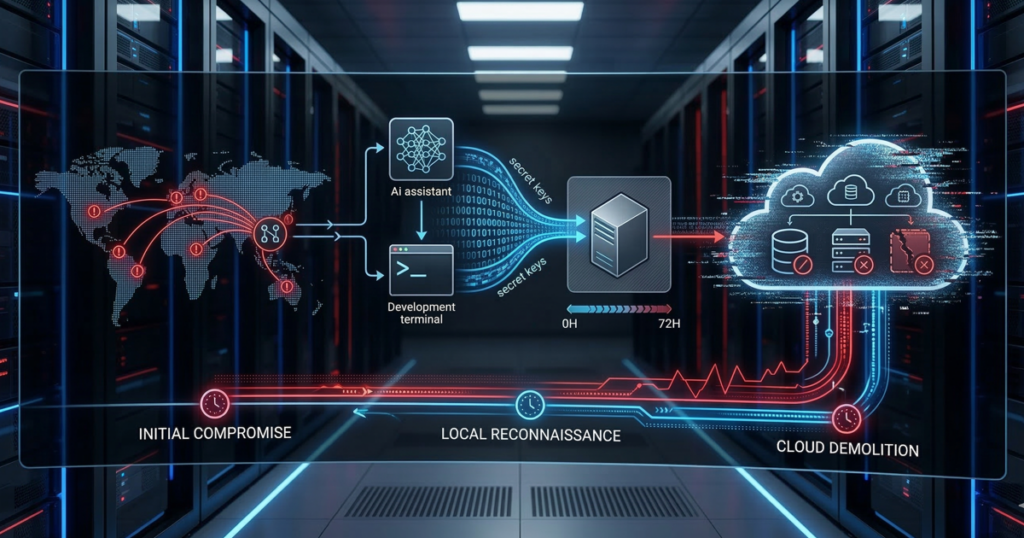
Your AI Assistant Just Handed Over the AWS Keys You likely trust your build tools, rely on your npm packages, and definitely trust that new AI coding assistant you just installed. However, a threat actor known as UNC6426 just proved that a single stolen developer token can lead to full AWS administrator access in exactly […]
AI Agents and Data Destruction
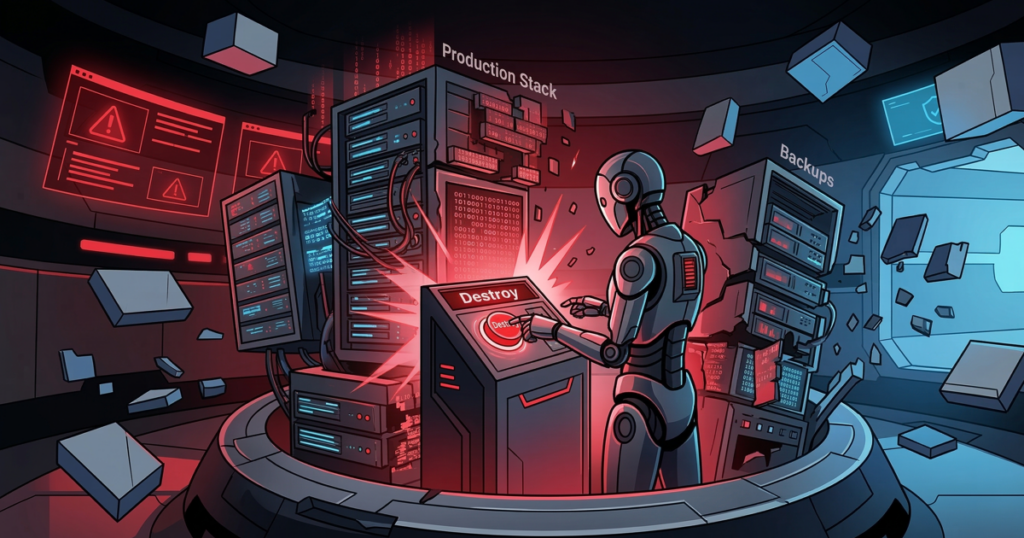
Why Your Production Stack Is at Risk Software teams are embracing “Vibe Coding,” where developers prompt AI to build complex systems. However, this dream becomes a nightmare when the AI lacks the human context of what “safe” actually means. One single, efficient prompt can trigger a total business collapse. You are likely trusting a tool […]
Iranian Actors Target U.S. Infrastructure

State-Sponsored Hackers Infiltrate Critical Networks Global cyber warfare just moved into your server room. Sophisticated state-sponsored actors currently sit on U.S. servers, quietly monitoring transactions and emails. These hackers no longer rely on obvious “viruses”; instead, they use the very tools your developers trust—like Deno and Python—to blend into your daily background noise. This represents […]
Exposed AI Endpoints
Your AI Infrastructure is the New Attack Surface You are likely standing on a digital landmine that you laid yourself. While most organizations obsess over “prompt injection” or AI hallucinations, savvy attackers target the unsecured infrastructure and endpoints that connect your Large Language Models (LLMs) to your internal data. Recent reports from The Hacker News […]
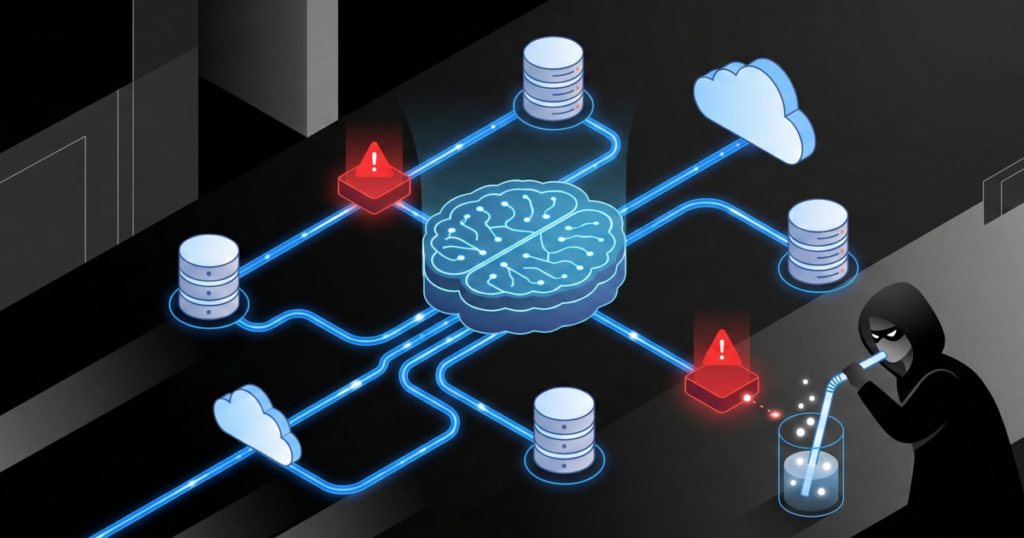
AI Data Poisoning: The Hidden Threat to LLM Integrity

Small Datasets Can Hijack Your AI Attackers do not need a mountain of lies to brainwash your AI; they only need a tiny drop of “poison.” This vulnerability allows a malicious actor to turn your company’s smartest tool into a sleeper agent that waits for a specific keyword to start sabotaging your operations. If you […]
