Adobe Acrobat Zero-Day Exploited in the Wild

Turning Trusted Documents Into Digital Weapons To every Small and Medium Business owner: Hackers are currently abusing a massive zero-day vulnerability in Adobe Acrobat and Reader. This isn’t a “what if” scenario; attackers are actively exploiting a document-based threat to hijack computers the moment a user opens a file. Your team opens dozens of PDFs […]
Docker Engine Vulnerability

Is Your Digital Bouncer Ignoring Intruders? Docker Engine security relies on robust isolation, but a critical flaw now allows attackers to walk right past your digital front door. You might invest in premium security plugins and strict container policies, but CVE-2026-34040 reveals that your “bouncer” stops checking IDs the moment a request looks slightly too […]
Chaos Malware Evolution

Enterprise Infrastructure Under Attack To every CTO, System Administrator, and Developer: The Chaos botnet just graduated from attacking home routers to compromising your high-performance enterprise hardware. We are not describing a theoretical update; the Chaos malware now actively targets 64-bit Linux servers, representing a massive tactical shift in the global threat landscape. Your server environment—the […]
Critical Root RCE Flaws Exposed in Telnet

Your Legacy Hardware is a Time Bomb A ghost is hiding in your server room, and it just unlocked the front door. While you spend your budget on modern AI firewalls, a 90s-era protocol is handing over the keys to your kingdom. We are tracking a 9.8 out of 10 critical severity rating for vulnerabilities […]
Exposed AI Endpoints
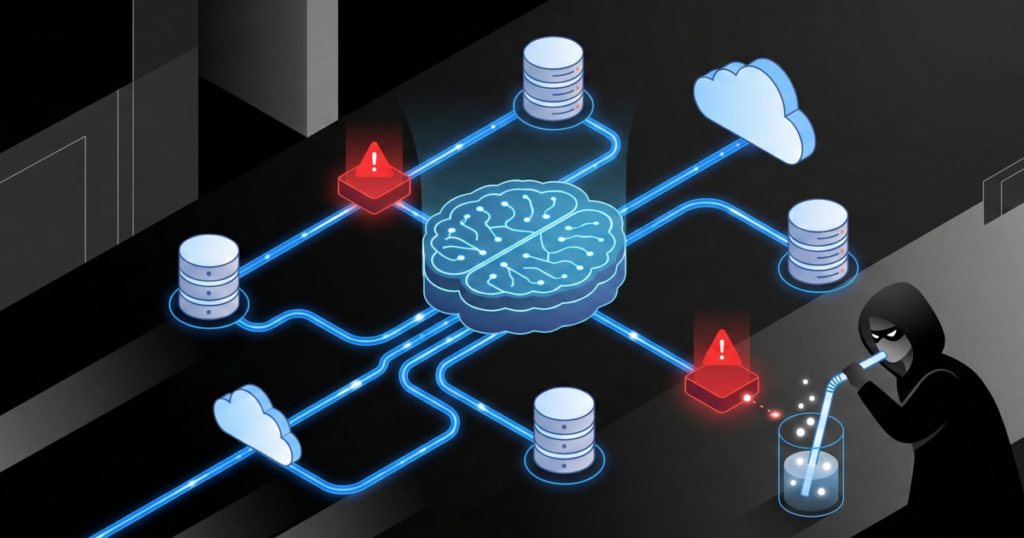
Your AI Infrastructure is the New Attack Surface You are likely standing on a digital landmine that you laid yourself. While most organizations obsess over “prompt injection” or AI hallucinations, savvy attackers target the unsecured infrastructure and endpoints that connect your Large Language Models (LLMs) to your internal data. Recent reports from The Hacker News […]
