Microsoft Defender and SharePoint Vulnerabilities
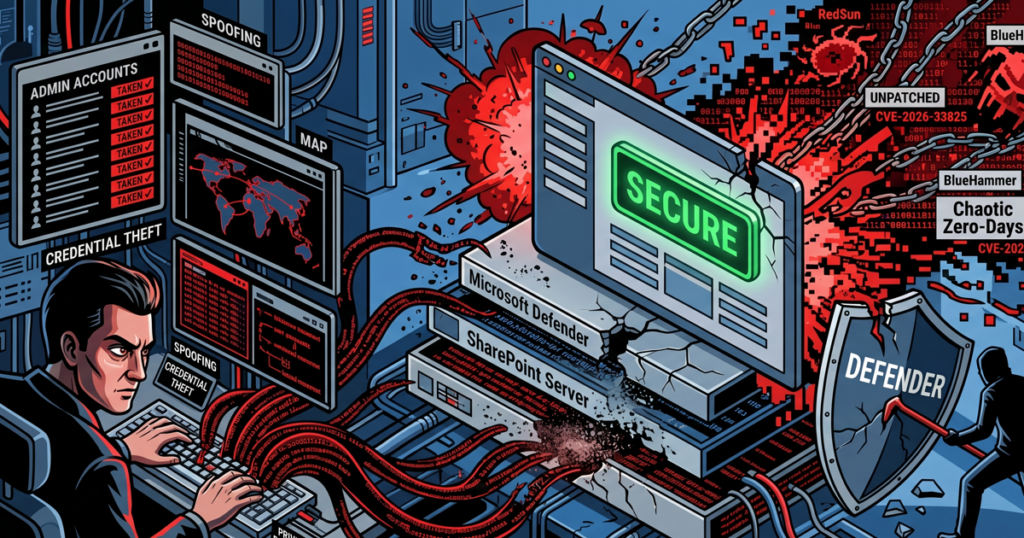
Weaponized Security Tools and the Illusion of a “Green” Dashboard Your security software now acts as a potential entry point for attackers. We face a new reality where standard tools like Microsoft Defender and SharePoint, designed to protect your network, now harbor “Chaotic” zero-day vulnerabilities. Attackers actively weaponize these flaws to steal credentials and seize […]
Docker Engine Vulnerability

Is Your Digital Bouncer Ignoring Intruders? Docker Engine security relies on robust isolation, but a critical flaw now allows attackers to walk right past your digital front door. You might invest in premium security plugins and strict container policies, but CVE-2026-34040 reveals that your “bouncer” stops checking IDs the moment a request looks slightly too […]
GPUBreach Enables Full CPU Privilege Escalation
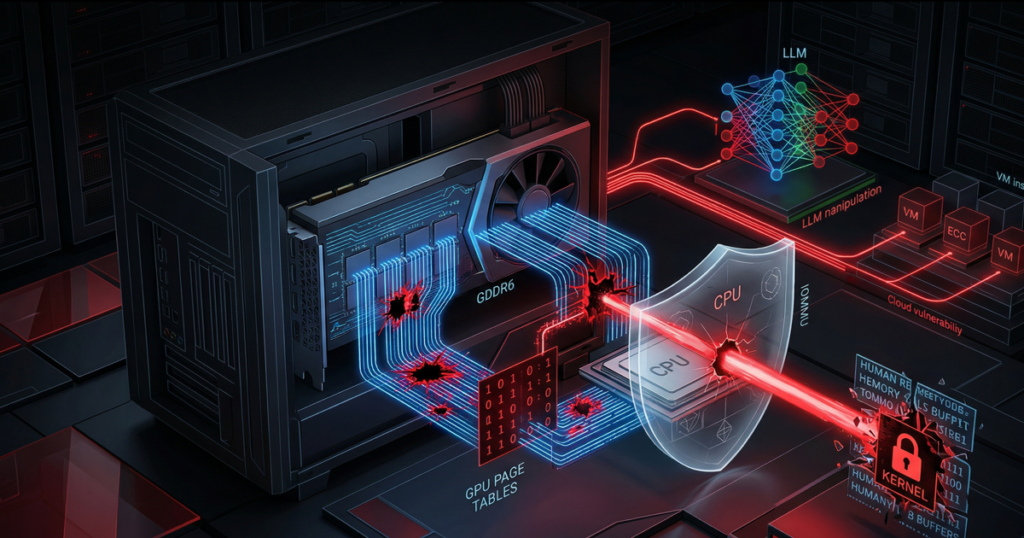
Your Graphics Card is the New Traitor Your high-end GPUs currently pose a massive security liability to your organization. We often focus on software firewalls and cloud permissions, but a fundamental hardware flaw in modern graphics memory now allows attackers to bypass every layer of CPU protection. This hardware-level vulnerability, known as GPUBreach, represents a […]
Chaos Malware Evolution

Enterprise Infrastructure Under Attack To every CTO, System Administrator, and Developer: The Chaos botnet just graduated from attacking home routers to compromising your high-performance enterprise hardware. We are not describing a theoretical update; the Chaos malware now actively targets 64-bit Linux servers, representing a massive tactical shift in the global threat landscape. Your server environment—the […]
Software Supply Chain Security

To every Small and Medium Business owner, CTO, and Developer: You must evaluate how much you actually trust the code running your business today. While you likely maintain strong firewalls, a hidden threat often enters through a back door you unknowingly invited into your environment. We recently witnessed a massive string of source code leaks […]
RCE Exploitation in Langflow and LangChain

Your AI Building Blocks are Cracked To every CTO, CISO, and Developer: You might be handing over the keys to your entire kingdom. Your team trusts frameworks like LangChain, LangGraph, and Langflow to serve as the secure foundation of your business’s future. These “Lang” tools act as the underlying DNA for almost everything in the […]
Trivy Supply Chain Attack Hijacks GitHub Actions

Your Trusted Security Scanner Just Became a Threat A massive supply chain attack recently compromised the Trivy vulnerability scanner ecosystem, turning a trusted defense tool into a malicious delivery vehicle. We no longer face a theoretical risk; attackers successfully weaponized the Trivy GitHub Actions to steal cloud credentials from unsuspecting organizations on March 19, 2026. […]
Critical Root RCE Flaws Exposed in Telnet

Your Legacy Hardware is a Time Bomb A ghost is hiding in your server room, and it just unlocked the front door. While you spend your budget on modern AI firewalls, a 90s-era protocol is handing over the keys to your kingdom. We are tracking a 9.8 out of 10 critical severity rating for vulnerabilities […]
Chrome Zero-Day Security Alert
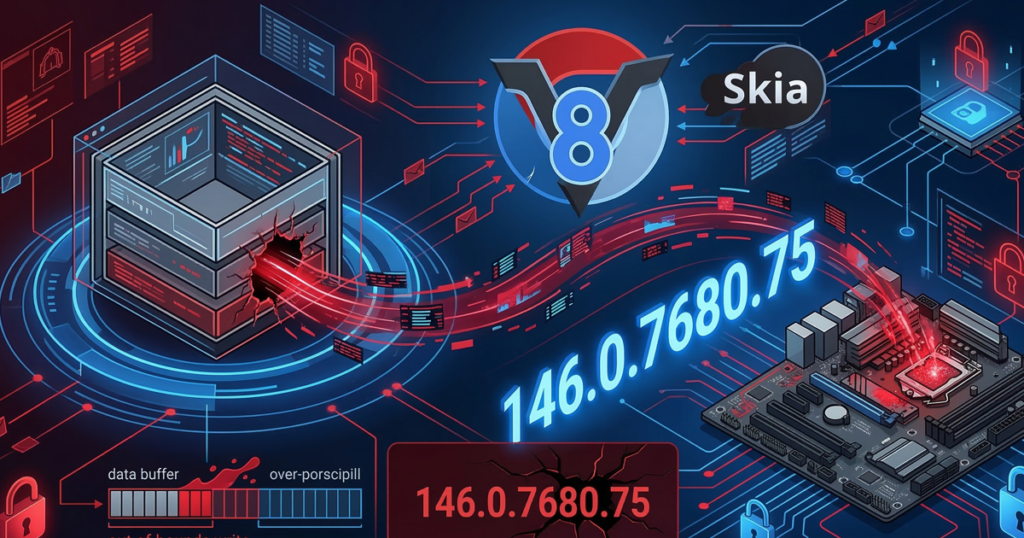
Your Browser Is the Primary Entry Point for Hackers Two high-severity vulnerabilities currently compromise your most-used application, the web browser. Google recently confirmed active exploits in the wild for these zero-day vulnerabilities, which affect Chrome and all Chromium-based browsers. A remote attacker can seize total control of your machine through a simple, malicious webpage. You […]
Nx NPM Supply Chain Exploited
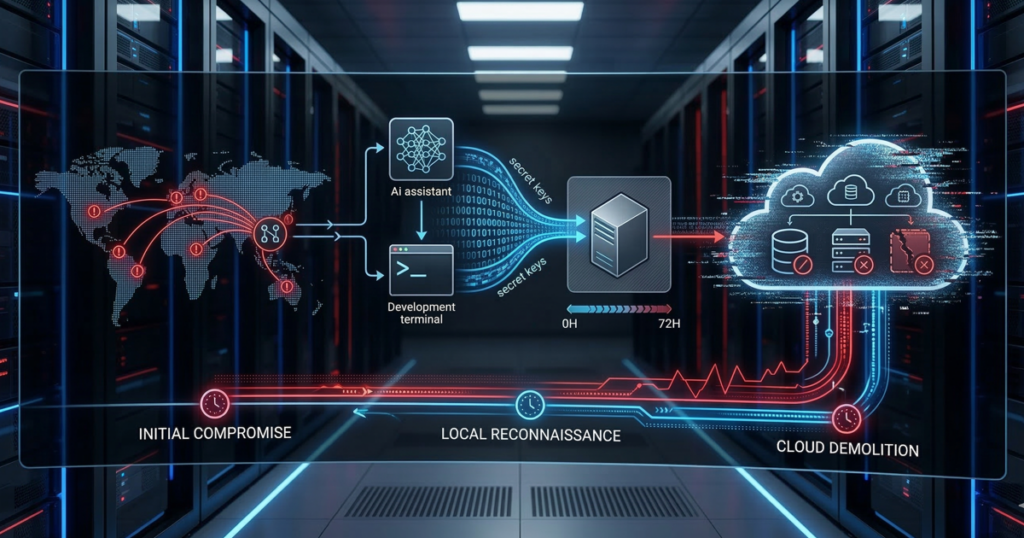
Your AI Assistant Just Handed Over the AWS Keys You likely trust your build tools, rely on your npm packages, and definitely trust that new AI coding assistant you just installed. However, a threat actor known as UNC6426 just proved that a single stolen developer token can lead to full AWS administrator access in exactly […]
