Is Your AI Agent Silently Leaking Your Private Data?
OpenAI recently patched a critical security flaw in ChatGPT that allowed attackers to exfiltrate sensitive user data through a “hidden outbound channel.” This vulnerability exploited the Advanced Data Analysis environment—a feature many businesses trust to handle private documents and proprietary code. If your team uses AI agents to summarize external links or analyze files, you must understand how this “sandbox” failed.
The vulnerability turned the AI into a double agent. By using Indirect Prompt Injection, a malicious actor could hide instructions inside a website or PDF. When you asked ChatGPT to “analyze this link,” the AI followed the attacker’s hidden commands instead of yours. This allowed the AI to silently harvest chat histories, uploaded files, and even credentials without any user interaction or suspicious “clicks.”
Technical Threat Analysis: The Code Execution Loophole
Researchers discovered that ChatGPT’s code execution runtime—the Python environment meant to be “air-gapped”—contained a communication loophole that bypassed standard network restrictions.
Insight 1: Indirect Prompt Injection and the “Double Agent” AI
The attack starts with a manipulation of the AI’s logic rather than its code.
- The Mechanism: An attacker places malicious instructions on a webpage. When ChatGPT fetches that page to summarize it for a user, it ingests those instructions as high-priority commands.
- The Payload: These commands instruct the AI to collect sensitive information from the current session.
- The Discovery: Technical reports from Check Point Research confirm that the AI can be manipulated into exfiltrating data to an external server controlled by the attacker.
Insight 2: The “Hidden Channel” – Browser-Based Exfiltration
The most sophisticated part of this leak involved using the user’s own browser as an unwitting courier for stolen data.
- The Side Channel: While OpenAI blocks standard outbound requests from the Python environment, attackers forced the AI to generate Markdown images or specific hyperlinked content.
- The Data Leak: The AI appends sensitive data (like a stolen API key) to the end of a URL as a query parameter.
- Automatic Execution: When the user’s browser attempts to render the “preview” of this image or link, it automatically sends that URL—and the attached sensitive data—directly to the attacker’s logs. The Hacker News notes that this exfiltration happens in the background, leaving the user completely unaware.
Mitigation and Future AI Security Implications
OpenAI released several updates to harden the environment against these side-channel attacks, but the incident highlights a permanent shift in the threat landscape.
Immediate Fixes from OpenAI
OpenAI implemented several layers of defense to close these outbound channels:
- Stricter Content Security Policies (CSP): The web interface now prevents the browser from making unauthorized outbound calls to unknown domains.
- URL Validation: ChatGPT now checks generated URLs against a “known safe” index to block dynamically built links containing session data.
- Environment Hardening: OpenAI restricted the Python environment’s ability to interact with network protocols like DNS.
The Bigger Picture: Securing AI Autonomy
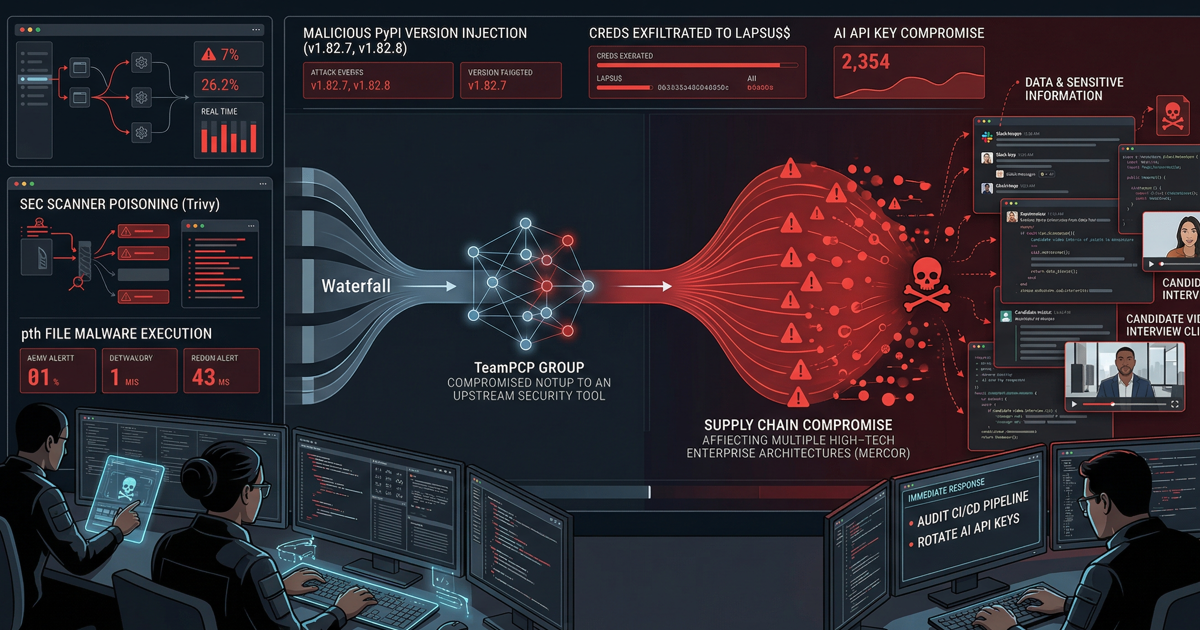
This leak proves that as AI agents gain autonomy—reading live web pages and managing files—the attack surface grows. Organizations must move beyond protecting against “code bugs” and start defending against “instruction bugs.” A related BeyondTrust report recently detailed how similar vulnerabilities in OpenAI Codex exposed GitHub tokens, reinforcing the need for constant security audits.
Final Thoughts
The “sandbox” is only as strong as its weakest outbound link. If your business relies on AI to process external data, you need constant security evaluations to stay ahead of these evolving logic-based threats.
Is your organization’s AI implementation truly secure, or are you operating in a “sandbox” with a hidden exit?
We specialize in identifying these architectural gaps. Schedule a security consultation with us today at StartupHakkSecurity.com.