To every Small and Medium Business owner, CTO, and Developer: You must evaluate how much you actually trust the code running your business today. While you likely maintain strong firewalls, a hidden threat often enters through a back door you unknowingly invited into your environment. We recently witnessed a massive string of source code leaks from industry giants like Anthropic, Checkmarx, and Axios, all occurring within a single ten-day window.
These incidents do not involve simple password guesses. Instead, attackers expose the very blueprints of proprietary software to the world. A single human error recently exposed fifty megabytes of internal data from a leading AI company. This trend signals a critical shift: the “high-trust” bubble of software development has officially burst.
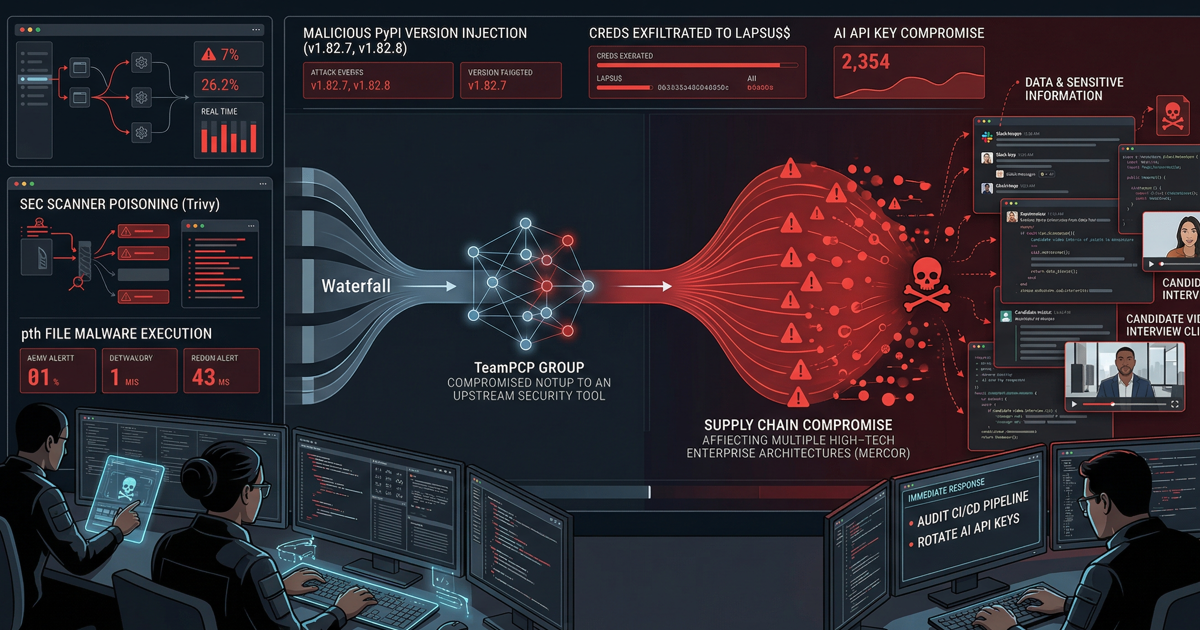
Technical Threat Analysis: Why the Supply Chain is Broken
The modern development lifecycle relies on a chain of trust that attackers now exploit with surgical precision.
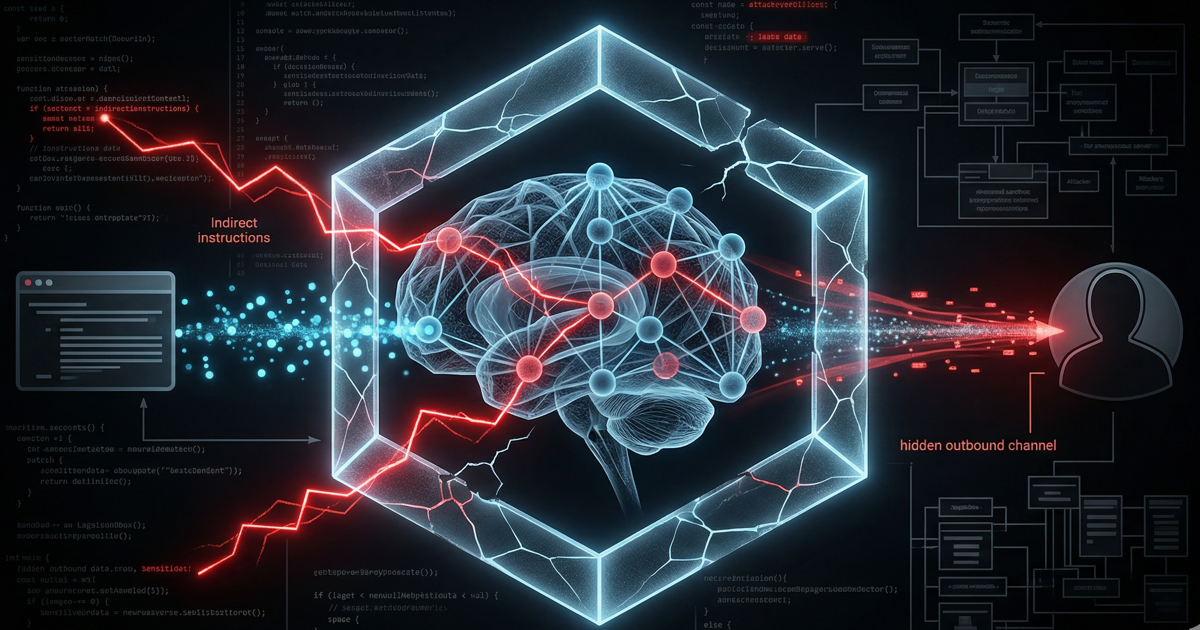
1. The Human Element in AI Development
The recent leak at Anthropic did not require a sophisticated hacking feat. Instead, a developer committed a simple human mistake by accidentally packaging internal code into a public registry. As companies rush to ship AI tools, the complexity of these builds skyrockets. These fast-paced environments often skip the basic “content checks” that would normally catch a massive file exposure. According to Runtime, AI coding agents actually amplify this risk by automating tasks that previously required a human eye for security. If a global leader like Anthropic accidentally publishes its source maps, every small business must audit its release process immediately.
2. The Developer Workstation as the New Perimeter
Security professionals historically focused on the server, but the target has now shifted to the developer’s laptop. Attackers view these workstations as “high-trust” zones with broad access and low visibility. Dark Reading points out that compromising one developer’s account—as seen in the Checkmarx incident—allows an intruder to slip malicious code into a project before the build even begins. This silent infection starts directly at the source of your intellectual property.
3. The Explosion of Secrets Sprawl
Organizations currently face a tidal wave of leaked credentials. Snyk reports that developers leaked a staggering 28 million secrets on GitHub in 2025 alone, representing a 34% jump. Attackers no longer bother with complex malware; they simply find your leaked API keys in a .env file and log in as a legitimate user. This makes traditional detection nearly impossible because the attacker mimics a trusted employee. When these keys end up in public build logs through tools like GitHub Actions, your entire CI/CD pipeline becomes a weapon against you.
Mitigation: Building Automated Guardrails
You cannot rely on the “hope” that your team avoids mistakes. You must implement structural changes to secure your organization.
- Implement Policy as Code: Shift your security strategy toward “Policy as Code.” Use tools like HashiCorp Vault to keep secrets out of your source code entirely. These systems inject credentials only at the specific moment the application needs them.
- Inventory Your Dependencies: Most of your software consists of third-party libraries. Veracode notes that over 60% of critical vulnerabilities originate in these dependencies. You must maintain a Software Bill of Materials (SBOM) to track every piece of code running in your stack.
- Shift Left Security: Follow the advice of Cycode and implement “Shift Left” security. Set up automated gatekeepers and pre-commit hooks. these tools block a developer from pushing code if the commit contains a secret or an oversized file.
Final Thoughts
The software supply chain is under a microscopic lens. Whether it is a human error in an AI build or a poisoned third-party library, the risks to small and medium businesses have never been higher. You must build security into the core of your development culture, not just bolt it on later.
Does your team have the visibility needed to prevent a major source code leak?
We can help! Schedule a consultation with our experts today at StartupHakkSecurity.com.